- Release notes
- Getting started
- Installation
- Configuration
- Integrations
- Authentication
- Working with Apps and Discovery Accelerators
- AppOne menus and dashboards
- AppOne setup
- TemplateOne 1.0.0 menus and dashboards
- TemplateOne 1.0.0 setup
- TemplateOne menus and dashboards
- TemplateOne 2021.4.0 setup
- Purchase to Pay Discovery Accelerator menus and dashboards
- Purchase to Pay Discovery Accelerator Setup
- Order to Cash Discovery Accelerator menus and dashboards
- Order to Cash Discovery Accelerator Setup
- Basic Connector for AppOne
- SAP Connectors
- Introduction to SAP Connector
- SAP input
- Checking the data in the SAP Connector
- Adding process specific tags to the SAP Connector for AppOne
- Adding process specific Due dates to the SAP Connector for AppOne
- Adding automation estimates to the SAP Connector for AppOne
- Adding attributes to the SAP Connector for AppOne
- Adding activities to the SAP Connector for AppOne
- Adding entities to the SAP Connector for AppOne
- SAP Order to Cash Connector for AppOne
- SAP Purchase to Pay Connector for AppOne
- SAP Connector for Purchase to Pay Discovery Accelerator
- SAP Connector for Order-to-Cash Discovery Accelerator
- Superadmin
- Dashboards and charts
- Tables and table items
- Application integrity
- How to ....
- Working with SQL connectors
- Introduction to SQL connectors
- Setting up a SQL connector
- CData Sync extractions
- Running a SQL connector
- Editing transformations
- Releasing a SQL Connector
- Scheduling data extraction
- Structure of transformations
- Using SQL connectors for released apps
- Generating a cache with scripts
- Setting up a local test environment
- Separate development and production environments
- Useful resources
Process Mining user guide
Introduction
This page describes how to set up LDAP to give Superadmin users and end users access to UiPath Process Mining. To enable LDAP for UiPath Process Mining you must specify the ldap object in the ExternalAuthenticationProviders setting the Server Settings.
LDAP for UiPath Process Mining is only supported with Microsoft Active Directory.
Configure LDAP Settings
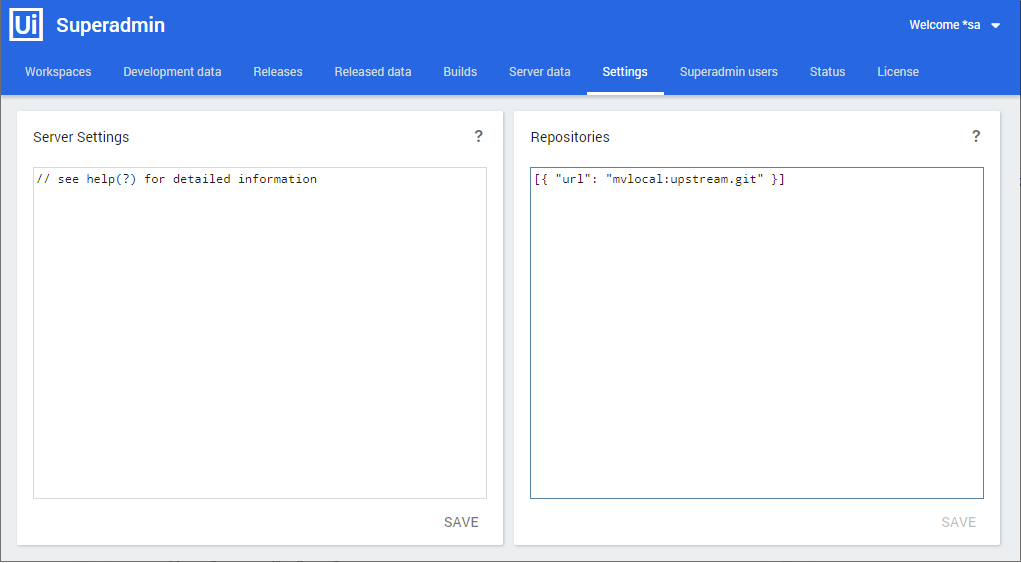
Go to the Settings tab of the Superadmin page of your UiPath Process Mining installation. See illustration below.
Add the required LDAP settings in the ExternalAuthenticationProviders setting of the Server Settings for the ldap object. Below is a description of the JSON keys of the ldap object:
| Key | Description |
|---|---|
| url | The LDAP url domain controller in the domain you want to use. This url needs to be accessible from the UiPath Process Mining server. Use the format: ldap://dc.company.domain.com. |
| base | The LDAP base distinguished name to authenticate users under. Use the format: DC=Company,DC=com . The exact name depends on the setup of the AD. |
| bindDN | The username of the AD user that is used to bind to the AD. This user should have the rights to query user groups for users that are allowed to login. Note: this user might need to be prefixed with the domain name, for instance: |
| bindCredentials | The password of the user specified in bindDN. See also Use a Credential Store . |
| search_query | Enables you to specify whether users can login with a different attribute than userPrincipalName . |
| tlsOptions | Enables you to specify additional options for use with LDAPS. ca : used to specify the certificate which should be used. rejectUnauthorized : set this to true . See also Set up Secure LDAP . |
See below for an example.
"ExternalAuthenticationProviders" {
"ldap": {
"url": "ldap://ldapserver",
"base": "DC=company,DC=local",
"bindDN": "username",
"bindCredentials": "password",
}
}
"ExternalAuthenticationProviders" {
"ldap": {
"url": "ldap://ldapserver",
"base": "DC=company,DC=local",
"bindDN": "username",
"bindCredentials": "password",
}
}
Click on SAVE to save the LDAP settings.
Press F5 to refresh the Superadmin page. This loads the new settings and enables users groups to be created based on these settings.