- Overview
- Apple Mail
- Apple Numbers
- Apple Scripting
- Excel
- Release Notes
- About the Excel activity package
- Project compatibility
- Supported character encoding
- Project settings
- Add or Update Excel Sensitivity Label
- Append Range
- Auto Fill
- Autofit Range
- Change Pivot Data Source
- Clear Sheet/Range/Table
- Copy/Paste Range
- Create Pivot Table
- Delete Column
- Delete Rows
- Delete Sheet
- Duplicate Sheet
- Export to CSV
- Fill Range
- Filter
- Filter Pivot Table
- Find First/Last Data Row
- Find/Replace Value
- For Each Excel Row
- For Each Excel Sheet
- Format As Table
- Format Cells
- Get Cell Color
- Get Excel Chart
- Get Excel Sensitivity Label
- Get Selected Range
- Insert Column
- Insert Chart
- Insert Rows
- Insert Sheet
- Invoke VBA
- Lookup
- Match Function
- Protect Sheet
- Read Cell Formula
- Read Cell Value
- Read Range
- Refresh Excel Data Connections
- Refresh Pivot Table
- Remove Duplicates
- Rename Sheet
- Run Spreadsheet Macro
- Save Excel File
- Save Excel File As
- Save Excel File As PDF
- Select Range
- Sort Range
- Text to Columns
- Unprotect Sheet
- Update Excel Chart
- Use Excel File
- VLookup
- Write Cell
- Write CSV
- Write DataTable to Excel
- Excel Application Scope
- Append To CSV
- Read CSV
- Write CSV
- Delete Column
- Filter Table
- Get Table Range
- Insert Column
- Sort Table
- Append Range
- Close Workbook
- Get Cell Color
- Read Cell
- Read Cell Formula
- Read Column
- Read Range
- Read Row
- Select Range
- Set Range Color
- Write Cell
- Write Range
- Save Workbook
- Create Table
- Get Workbook Sheet
- Get Workbook Sheets
- Refresh Pivot Table
- Create Pivot Table
- Get Selected Range
- Copy Sheet
- Delete Range
- Auto Fill Range
- Copy Paste Range
- Execute Macro
- Insert/Delete Columns
- Insert/Delete Rows
- Invoke VBA
- LookUp Range
- Remove Duplicates Range
- Excel Process Scope
- Append Range Workbook
- Create New Workbook
- Create Pivot Table Workbook
- Get Cell Color Workbook
- Get Sheets Workbook
- Get Table Range Workbook
- Insert Chart Workbook
- Read Cell Formula Workbook
- Read Cell Workbook
- Read Column Workbook
- Read Range Workbook
- Read Row Workbook
- Set Range Color Workbook
- Update Chart Workbook
- Write Cell Workbook
- Write Range Workbook
- Manage CSV Files
- Filter CSV Files
- Verify CSV Files
- Compare CSV Files
- Sort Data in Excel Files
- Filter and Delete Rows in Excel Files
- Read, Write, and Append Data in Excel
- Table Functions
- Read From Excel Files
- Manage Multiple Excel Files
- Filter Excel files by cell color
- Verify Excel Workbook Data
- Compare Numeric Values
- Interpret Excel Results
- Manage Range Selection
- Manipulate Range Selections
- Manage Pivot Tables
- Manage Databases in Excel
- Google Workspace
- Release notes
- About the Google Workspace activities package
- Project compatibility
- Project settings
- Google Workspace HTTP Request
- Run Script
- Apply File Labels
- Clear File Label Fields
- Copy File
- Create Folder
- Delete File or Folder
- Delete File or Folder Permission
- Download File
- For Each File or Folder
- Get Drive Labels
- Get File or Folder Info
- Get File Labels
- Get File/Folder
- Get File List
- Get File or Folder Permissions
- Move File
- Remove File Labels
- Rename File or Folder
- Share File or Folder
- Update File or Folder Permission
- Upload Files
- Apply Gmail Labels
- Archive Email
- Delete Email
- Download Email
- Download Email Attachments
- For Each Email
- Forward Email
- Get Email by ID
- Get Email List
- Get Gmail Labels List
- Get Email Thread
- Get Newest Email
- Get Single Gmail Label
- Mark Email as Read/Unread
- Move Email
- Remove Gmail Labels
- Reply to Email
- Send Email
- Turn On Automatic Replies
- Turn Off Automatic Replies
- Wait for Calendar Event Created and Resume
- Wait for Calendar Event Received and Resume
- Wait for Calendar Event Replied and Resume
- Wait for Calendar Event Updated and Resume
- Wait for Email Received and Resume
- Wait for Email Sent and Resume
- Wait for File Created and Resume
- Wait for File Updated and Resume
- Wait for Folder Created and Resume
- Wait for Sheet Created and Resume
- Wait for Sheet Cell Updated and Resume
- Wait for Row Added to the Bottom of a Sheet
- Wait for Task Created and Resume
- Wait for Task Completed and Resume
- Add Attendee
- Create Event
- Delete Event
- Modify Event
- Search Events
- Use Google Drive
- Share File
- Delete File Permission
- Get File Permissions
- Update File Permission
- Copy File
- Create Folder
- Delete File
- Download File
- Find Files and Folders
- Get File Info
- Move File
- Upload File
- Create Document
- Create New Spreadsheet
- Get Mail Messages
- Send Mail Messages
- Change Labels
- Use Google Spreadsheet
- Add Delete Columns
- Add Delete Rows
- Auto Fill Range
- Add New Sheet
- Append Row
- Batch Spreadsheet Updates
- Copy Sheet
- Copy Paste Range
- Delete Range
- Delete Sheet
- Get Cell Color
- Get Sheets
- Read Cell
- Read Column
- Read Range
- Read Row
- Rename Sheet
- Write Cell
- Write Range
- Clear Range
- Download Spreadsheet
- Use Google Document
- Batch Document Updates
- Get Document
- Get Text Index
- Insert Text
- Replace Text
- Read All Text
- Create Script Project
- Get Project Content
- Upload Script File
- Create Deployment
- Run Script
- Mail
- Microsoft 365
- Release notes
- About the Microsoft 365 activity package
- Project compatibility
- Project settings
- Microsoft 365 HTTP Request
- List All Records
- Assign Sensitivity Label
- Create Folder
- Copy File/Folder
- Delete File or Folder
- Download File
- File Check-in/Check-out
- For Each File or Folder
- Get File/Folder
- Get File or Folder Metadata
- Get Sensitivity Labels
- Get File or Folder List
- Move File/Folder
- Rename file or folder
- Share File/Folder
- Upload Files
- Update File or Folder Metadata
- Archive Email
- Assign Sensitivity Label To Email
- Delete Email
- Download Email
- Download Email Attachments
- For Each Email
- Forward Email
- Get Email By ID
- Get Email Folders List
- Get Email List
- Get Email Thread
- Get Newest Email
- Mark Email as Read or Unread
- Move Email
- Reply to Email
- Send Draft Email
- Send Email
- Set Email Categories
- Turn On Automatic Replies
- Turn Off Automatic Replies
- Wait for Calendar Event Created and Resume
- Wait for Calendar Event Received and Resume
- Wait for Calendar Event Replied and Resume
- Wait for Calendar Event Updated and Resume
- Wait for Cell in Worksheet Updated and Resume
- Wait for Email Received and Resume
- Wait for Email Sent and Resume
- Wait for File Created and Resume
- Wait for File Updated and Resume
- Wait for Row Added to the Bottom of a Table and Resume
- Wait for List Item Added and Resume
- Wait for List Item Updated and Resume
- Wait for Worksheet Created and Resume
- Connections
- AddEmailCategories
- ArchiveEmail
- DeleteEmail
- DownloadEmail
- DownloadEmailAttachment
- DownloadEmailAttachments
- ForwardEmail
- GetEmail
- GetEmailAttachmentsInfo
- GetEmails
- GetMailFolders
- GetNewestEmail
- MarkEmailAsRead
- MarkEmailAsUnread
- MoveEmail
- RemoveEmailCategories
- ReplyToEmail
- SendEmail
- TurnOffAutomaticReplies
- TurnOnAutomaticReplies
- Merge multiple sheets into a new summary Excel sheet
- Automatically accept calendar invites from your manager
- Move files to dedicated folders by type
- Verify if new employment documents (I9 and ID) match
- Add new customers to a SharePoint List
- Delete SharePoint List items newer than yesterday
- Notify me on Slack when an important Outlook Email is received
- Include creation date in new OneDrive file names
- Notify me by email when a new file is created
- Microsoft 365 Scope
- Add Sheet
- Append Range
- Clear Range
- Copy Range
- Copy Sheet
- Create Workbook
- Delete Range
- Delete Sheet
- Get Cell Color
- Get Sheets
- Read Cell
- Read Column
- Read Range
- Read Row
- Rename Sheet
- Write Cell
- Write Range
- Set Range Color
- Create Table
- Get Table Range
- Insert Column
- Delete Column
- Insert Rows
- Delete Rows
- VLookup Range
- Use OneDrive & SharePoint
- Copy File/Folder
- Create Folder
- Delete File/Folder
- Download File
- Export File as PDF
- Find Files And Folders
- Get File/Folder
- Move File/Folder
- Upload File
- Share File/Folder
- For Each File/Folder
- Forward Mail
- Find Meeting Times
- Get Mail
- Move Mail
- Send Mail
- Reply to Mail
- Delete Mail
- Set Mail Categories
- Add Attachment
- Add Attendee
- Add Location
- Create Event
- Delete Event
- Get Calendars
- Modify Event
- RSVP
- Search Events
- Create Group
- Delete Group
- Get Group
- List Groups
- Create Bucket
- Delete Bucket
- List Buckets
- List Bucket Tasks
- Create Plan
- Get Plan
- List Plans
- Create Task
- Delete Task
- Get Task
- List Tasks
- Update Task
- For Each List
- Get List Info
- For Each List Item
- Delete List Item
- Add List Items
- Update List Item
- Get List Items
- Authentication troubleshooting
- AADSTS50011: Redirect URI mismatch
- AADSTS50076: Using multifactor authentication
- AADSTS50079: The user is required to use multifactor authentication
- AADSTS500113: No reply address registered for the application
- AADSTS900971: No reply address provided
- AADSTS65001: The user or administrator has not consented to use the application
- AADSTS65004: User declined to consent to access the app
- AADSTS7000218: The request body must contain the following parameter: client_assertion or client_secret
- AADSTS700025: Client is public so neither 'client_assertion' nor 'client_secret' should be presented
- AADSTS70002: InvalidClient - Error validating the credentials
- AADSTS7000215: Invalid client secret provided
- AADSTS50055: The password is expired
- AADSTS700082: The refresh token has expired due to inactivity
- AADSTS50194: Application is not configured as a multitenant application
- AADSTS53003: Access has been blocked by Conditional Access policies
- Mail troubleshooting
- Calendar troubleshooting
- Files troubleshooting
- Sheets troubleshooting
- Presentations
- Release Notes
- About the Presentations activity package
- Project compatibility
- Add or Update Powerpoint Sensitivity Label
- Add Data Table to Slide
- Add File to Slide
- Add Image or Video to Slide
- Add New Slide
- Add Text to Slide
- Copy Paste Slide
- Create New PowerPoint Document
- Delete Slide
- Format Slide Content
- Get Powerpoint Sensitivity Label
- Paste Item Into Slide
- Replace Text in Presentation
- Run Presentation Macro
- Save PowerPoint File As
- Save Presentation as PDF
- Use PowerPoint Presentation
- Word
- Release Notes
- About the Word activities package
- Project compatibility
- Word Application Scope / Use Word File
- Add or Update Word Sensitivity Label
- Add Hyperlink to Document
- Add Picture
- Append Text
- Create New Document
- Get Word Sensitivity Label
- Insert DataTable in Document
- Paste Chart/Picture Into Document
- Read Text
- Replace Picture
- Replace Text in Document
- Save Document As
- Save Document as PDF
- Set Bookmark Content
- Set Content Property

Productivity activities
Microsoft 365 Scope
UiPath.MicrosoftOffice365.Activities.Office365ApplicationScope
Description
Uses the Microsoft identity platform to establish an authenticated connection between UiPath and your Microsoft 365 application. This authenticated connection enables a Robot to call the Microsoft Graph API to read and write resources on your behalf.
Starting with version 2.5.5, you can use the newer Microsoft 365 activities inside the Scope activity. To learn how to use the Integration Service activities with Microsoft 365 Scope, check How to use Microsoft 365 activities without Integration Service connections.
Project compatibility
Windows - Legacy | Windows
Configuration
This page explains the authentication parameters available in the Microsoft 365 Scope activity. For more details regarding each authentication option, check the How to connect to Microsoft 365 activities guide.
To start configuring this activity, you must first select a connection method. Depending on the selected method, different fields are then displayed in the Properties panel.
- Connection method - Select the connection method you want to use. Options available in the dropdown menu are:
- Properties Panel - Configure the connection details in the Properties panel.
- Asset - Use Orchestrator text or credential assets, or both. We recommend you use this option.
Asset connection method
When you select this option, most of the authentication fields usually displayed in the Properties panel are hidden, because the authentication information is stored inside the asset.
-
Connection assets - Browse Orchestrator folders to select an asset. This field supports
IResourcevariables. Select the Manage Assets button to open Orchestrator. The list of available assets depends on the Orchestrator your Studio and Robot are connected to.You can use the asset at design time. In addition, the asset can be of text type only.- Use the Plus button menu to select Reload Assets if you've updated your assets in Orchestrator. Note that if you add a new asset in Orchestrator while using Studio Desktop, it will not be available straightaway in the Scope activity.
-
Check the asset format in How to use Microsoft 365 activities without Integration Service connections.
Depending on the authentication type configured in the asset, you must also configure the following fields available in the Properties panel:
Authentication
- Impersonated User Email Address - The email address of the impersonated user. Used for Application ID and Secret and Application ID and Certificate authentication methods.
Username and Password (Unattended)
- Username - The username of your Microsoft 365 account. Used for Username and Password authentication method.
- Password - The password of your Microsoft 365 account.
Common
- TimeoutMS - Specifies the amount of time to wait (in milliseconds) for the interactive authentication (consent dialogue box) to complete before an error is thrown. This field supports only integer and
Int32variables. The default value is 30000ms (30 seconds).
Runtime
- Runtime connection assets - Browse to select an asset. This field allows you to select a different asset for runtime. Use the Plus button menu to select Relative path and enter the full path of the Orchestrator asset containing connection details. We recommend you to use a credential asset in this field, but you can also use a text asset. The JSON value must be set in the password field for credential assets. This value is optional and, if left blank, the design time values will be used at runtime.
Properties Panel connection method
When you select this option, you must configure the authentication fields available in the Properties panel.
First, configure the following fields:
- Connections - Select an account from the list. You can add, delete, and choose what connections to use.
- Authentication Scopes
- Check the Using the Authentication Scopes wizard section below.
Using the Authentication Scopes wizard
This wizard replaces the Services parameter available in previous versions of this package. The Authentication Scopes wizard is available when you use Interactive token authentication.
The Scope activity incorporates a universal permissions selector, offering a clear picture of all the used authentication scopes, which the activities need in order to work correctly.
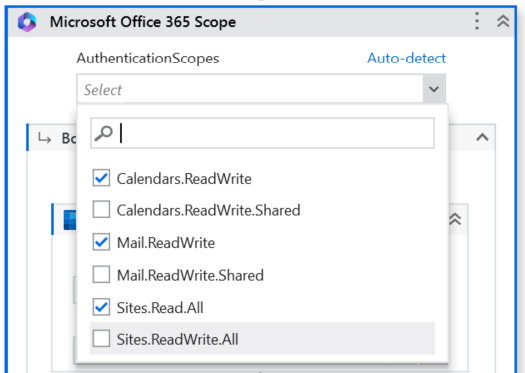
All children activities included in the Microsoft 365 Scope activity are automatically detected as required scopes.
If no scopes are manually selected from the Scopes wizard, the Auto-detect function is applied by default at runtime, and the need for configuring the wizard is eliminated. All the minimum required scopes are selected at runtime.
You can also add a scope manually after adding a child activity to Microsoft 365 Scope.
Next, you must select the Authentication Type from the Properties panel and configure the fields required for your preferred authentication method. The sections below list the fields available under each menu.
Authentication
-
Authentication Type - The type of authentication required for your registered application. Select one of the five options: Interactive token, Integrated Windows Authentication (IWA), Username and Password, Application ID and Secret, or Application ID and Certificate. The default value is Interactive Token.
-
Environment - The environment. Either Azure Global or national clouds that are unique and separate environments from Azure Global. Select one of the five options: Default, Global, China, Germany or USGovernment. The default value is Global.
-
Application ID - The unique application (client) ID assigned by the Azure Active Directory when you registered your app during setup. The application (client) ID represents an instance of a Microsoft 365 application.
-
Tenant - The unique directory (tenant) ID assigned by the Azure Active Directory when you registered your app during setup. Required for multi-tenant applications and Integrated Windows Authentication. The directory (tenant) ID can be found in the overview page of your registered application (under the application (client) ID).
-
Connection Data Store Location - A drop-down list that specifies where the token response gets stored. The available property values are Local disk, Orchestrator, or Never store.
- Local disk - The connection tokens are stored in a local folder on the machine. The same connection can be used in multiple processes on the same machine.
- Orchestrator - The connection tokens are stored in Orchestrator as assets in a specified folder. The same connection can be used in multiple processes on multiple machines as long as it has access to the specified Orchestrator folder.
- Never store - The connection tokens are never stored.
Note:The O365 storage solution is different than the GSuite one due to technical limitations. O365 stores all accounts in a single file in Orchestrator, while GSuite stores one file per account.
-
Connection Orchestrator Folder Path - The Orchestrator folder where the operations occur. Leave empty if Modern folders are not enabled. For more details, check About Folders in the Orchestrator guide.
-
Impersonated User Email Address - The email address of the impersonated user. Used in unattended scenarios for Application ID and Secret and Application ID and Certificate authentication methods.
Interactive token
This is the same authentication method that Integration Service supports either through the UiPath Public App or the Bring your own app method.
For details, check Interactive token.
- OAuth Application - Indicates the application (client) to be used. This field supports only
OAuthApplicationvariables. Select one of the two options:- UiPath - Default. When you want to use the application created by UiPath (UiPath Public App registration). If selected, the ApplicationID and Tenant fields provided in the Authentication section are ignored.
- Custom - When you want to create your own application with specific permissions. In this case, you must set a value for the Application ID field. Check Custom OAuth Application registration - Bring your own app (BYOA).
- Use broker - Set this option to True to use the Windows Authentication Manager (WAM) broker for interactive authentication. This option provides a more integrated authentication experience on Windows.
- OAuth2User - The email of the user who will log in through the interactive token.
Application ID and Certificate (Unattended)
For details, check Application ID and Certificate.
- Certificate As Base64 - The Base64 representation of the certificate.
- Certificate Password - An optional password that may be required to use the certificate, as a
Secure String.
Application ID and Secret (Unattended)
For details, check Application ID and Secret.
- Application Secret - The secret string that the application uses to provide its identity.
- Secure Application Secret - The Application (client) secret, as a
SecureString.
Username and Password (Unattended)
For details, check Username and Password.
Microsoft has deprecated Basic Authentication for Exchange online. This impacts some of our activities, such as Microsoft Office365 Scope. We recommend using the OAuth protocol in the activities that support it.
- Password - The password of your Microsoft 365 account.
- Secure Password - The password of your Microsoft 365 account, as a
SecureString. - Username - The username of your Microsoft 365 account.
Common
- TimeoutMS - Specifies the amount of time to wait (in milliseconds) for the interactive authentication (consent dialogue box) to complete before an error is thrown. This field supports only integers and
Int32variables. The default value is 30000ms (30 seconds) (not shown). - ContinueOnError - If set, continue executing the remaining activities even if the current activity has failed.
Troubleshooting
If you encounter any issues with authentication, check Troubleshooting - Authentication.