- Démarrage
- Meilleures pratiques
- Locataire
- À propos du contexte du locataire
- Recherche de ressources dans un locataire
- Gestion des Robots
- Connexion des Robots à Orchestrator
- Enregistrement des identifiants du Robot dans CyberArk
- Stockage des mots de passe de l’Unattended Robot dans Azure Key Vault (lecture seule)
- Stockage des informations d’identification de l’Unattended Robot dans HashiCorp Vault (lecture seule)
- Stockage des informations d'identification du robot Unattended dans AWS Secrets Manager (lecture seule)
- Suppression des sessions Unattended déconnectées et qui ne répondent pas
- Authentification du Robot
- Authentification du Robot avec les informations d'identification du client
- Configurer les capacités d’automatisation
- Solutions
- Audit
- Paramètres
- Registre
- Cloud Robots
- Cloud robots overview
- Exécution d'automatisations Unattended à l'aide de Cloud Robots - VM
- Téléchargement de votre propre image
- Réutilisation des images de machines personnalisées (pour les pools manuels)
- Réinitialisation des informations d'identification d'une machine (pour les pools manuels)
- Surveillance
- Mises à jour de sécurité
- Demander un essai
- Questions fréquemment posées
- Configuration du VPN pour les robots du cloud
- Configurer une connexion ExpressRoute
- Diffusion en direct et contrôle à distance
- Robots Automation Suite
- Contexte des dossiers
- Processus (Processes)
- Tâches (Jobs)
- Apps
- Déclencheurs (Triggers)
- Journaux (Logs)
- Surveillance
- Index
- Files d'attente (Queues)
- Actifs
- À propos des actifs
- Gestion des actifs dans Orchestrator
- Gestion des actifs dans Studio
- Stockage des ressources dans Azure Key Vault (lecture seule)
- Stockage des ressources dans HashiCorp Vault (lecture seule)
- Stockage des ressources dans AWS Secrets Manager (lecture seule)
- Stocker des ressources dans Google Secret Manager (lecture seule)
- Connexions
- Règles métier
- Compartiments de stockage
- Serveurs MCP
- Tests d'Orchestrator
- Service de catalogue de ressources
- Intégrations
- Résolution des problèmes

Guide de l'utilisateur d'Orchestrator
Managing credential proxies
Vous pouvez créer et gérer des proxys pour vos propres magasins d'informations d'identification personnalisés, ce qui vous permet de contrôler individuellement la sécurité de vos informations d'identification.
Type de proxy
Vous pouvez choisir entre ces deux types :
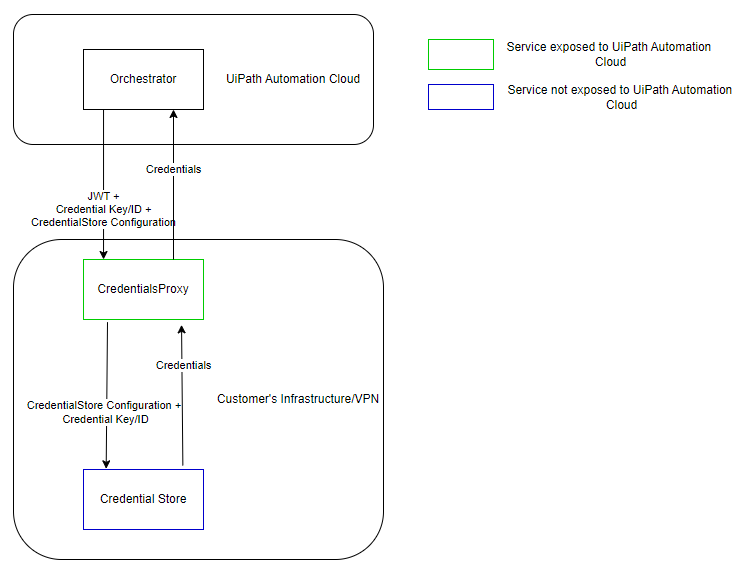
- Connected proxy (Managed by Orchestrator)
- when a robot requests credentials, Orchestrator retrieves them from the proxy and passes them on to the robot.
Figure 1. Connected proxy architecture
- Disconnected proxy (Managed by the proxy service) - when a robot requests credentials, they are retrieved directly from the proxy, without having to go through Orchestrator. This type is only compatible with Robots version 23.10+.
Figure 2. Disconnected proxy architecture 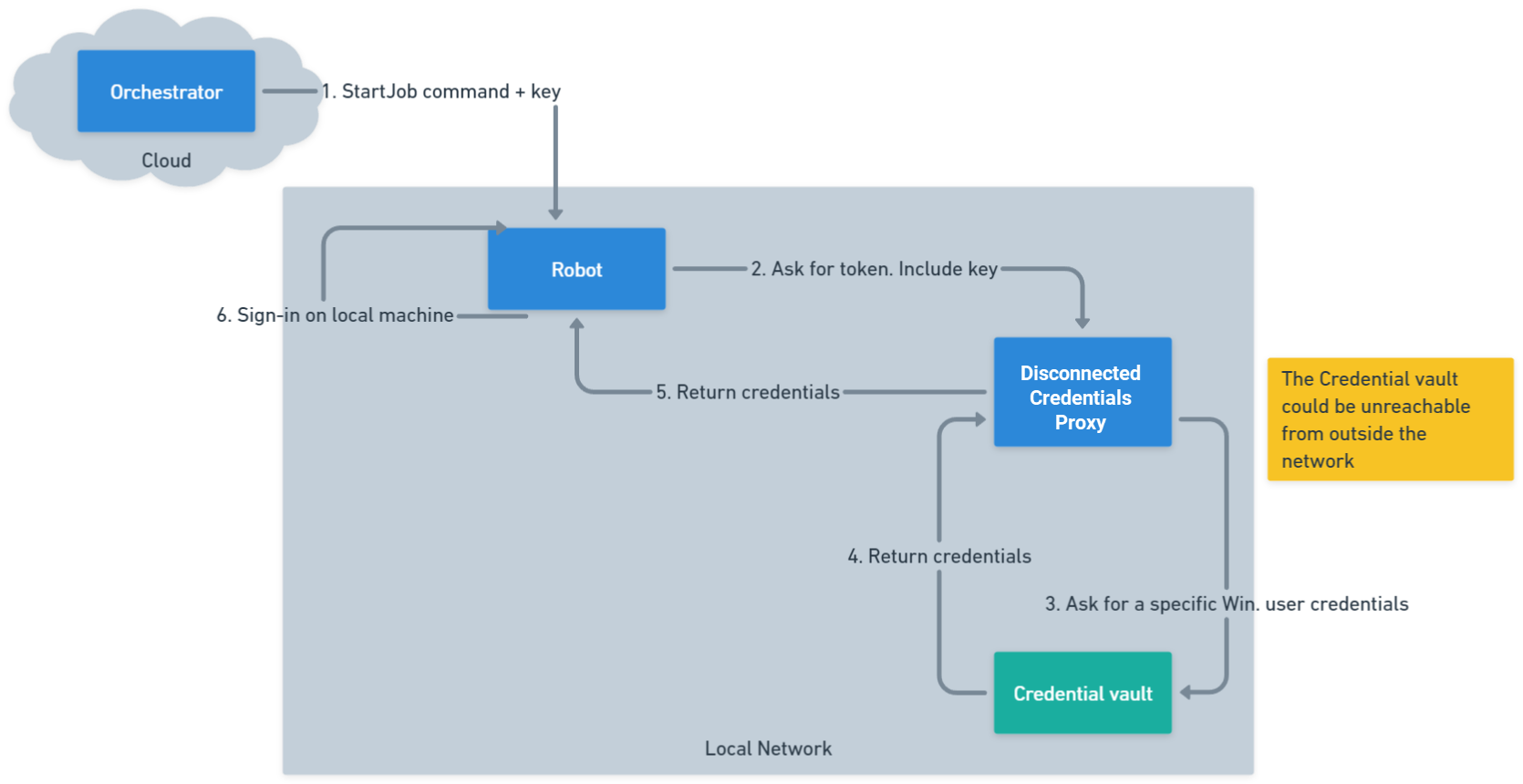
- The disconnected credentials proxy is only available if you are on the Enterprise - Advanced licensing plan.
- If you want to retrieve disconnected proxy credentials, you need to use the following minimum versions: 2.0.1 for the proxy, and 24.3 for the System Activities pack.
Configuration déconnectée
Dans la configuration déconnectée, le service Orchestrator Credentials Proxy fonctionne de manière semblable à celui de la configuration connectée, à quelques différences clés près.
Spécifiez dans le fichier appsettings.json que le proxy doit démarrer dans son mode déconnecté. Pour ce faire, sous AppSettings, définissez le paramètre CredentialsProxyType sur la valeur Disconnected.
Cela indique au proxy de faire les choses un peu différemment au démarrage et de lire la configuration de son magasin sécurisé dans le fichier appsettings.json. Si le paramètre est manquant ou si la valeur est différente, le proxy démarre en mode connecté.
Dans le fichier appsettings.json, spécifiez que le proxy doit démarrer en mode déconnecté. Pour ce faire, sous AppSettings, définissez le paramètre CredentialsProxyType sur la valeur Disconnected.
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
Cela indique au proxy de faire les choses un peu différemment au démarrage et de lire la configuration de son magasin sécurisé dans le fichier appsettings.json. Si le paramètre est manquant ou si la valeur est différente, le proxy démarre en mode connecté.
Configurations du magasin sécurisé
Chaque entrée de configuration doit contenir :
- Key: unique identifier used in Orchestrator when linking stores. This must be unique in the list of configurations
- Type: the type of secure store (such as Azure Key Vault, BeyondTrust, CyberArk, HashiCorp Vault, InMemory, and others).
- Context: the data needed by the Secure Store implementation, which varies depending on the store type.
Examinez l'exemple de configuration de magasin sécurisé suivant :
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
The SecureStoreConfigurations parameter is an array of configurations so you can have as many configurations as you want. Multiple configurations of the same type are supported, as long as the Key values are unique.
Validation au démarrage
Lorsqu'il s'exécute en mode déconnecté, le proxy effectue une validation au démarrage :
- Valide que les configurations requises existent dans
appsettings.json. - Vérifie qu'aucune clé en double ne se trouve dans
SecureStoreConfigurations. - Confirme que toutes les valeurs
Typesont valides. - Valide la connectivité du coffre (appels
ValidateContextAsyncpour chaque magasin).
Paramètres du niveau proxy
Certains magasins d'informations d'identification sécurisés nécessitent une configuration au niveau de l'hôte, qui doit être spécifiée dans appsettings.Production.json :
- CyberArk: settings like
CLIPasswordSDKExePath,UsePowerShellCLI, andAdditionalAllowedCharactersmust be defined underAppSettings.{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... } - CyberArkCCP: may require
Plugins.SecureStores.CyberArkCCP.KeyStorageFlags = "MachineKeySet".{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }
Configuration test examples
Examinez les appsettings.Production.json exemples pratiques suivants.
Avant d’apporter des modifications au fichier appsettings.Production.json, assurez-vous de créer une sauvegarde du fichier d’origine. Cela vous permet de restaurer facilement la configuration initiale ou de comparer les modifications si des problèmes surviennent pendant la configuration.
Exemple 1 : basique
Configuration avec coffre BeyondTrust et Azure Key Vault :
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
Exemple 2 : journaux supplémentaires et plusieurs configurations
Inclut plusieurs coffres et la journalisation avancée.
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
Exemple 3 : chemin d'accès personnalisé au journal et InMemoryStore
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
Création d'un Credentials Proxy
Once you have installed the Orchestrator Credentials Proxy, you can create a custom proxy, which holds your custom credential stores.
Figure 3. Add Credentials Proxy page 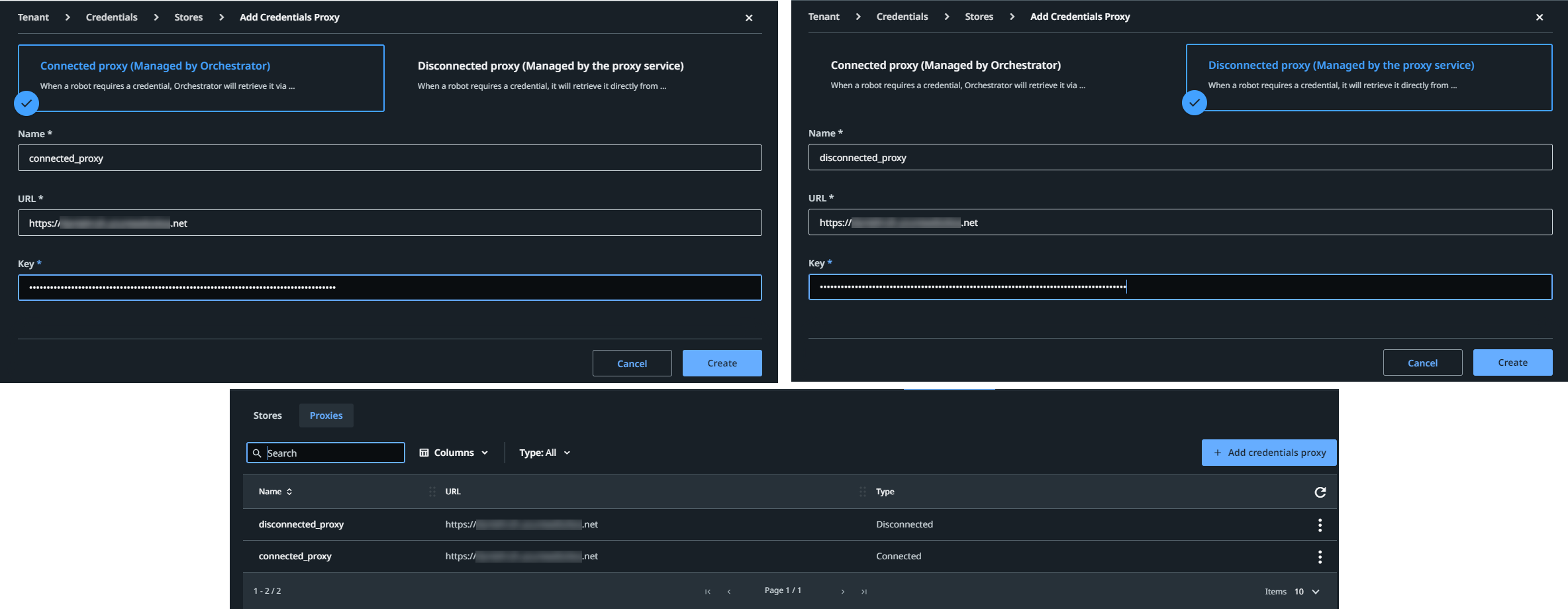
Pour ce faire, effectuez les étapes ci-dessous :
- At the tenant level, select Credentials > Proxies > Add Credentials Proxy. The Add Credentials Proxy window is displayed.
- Choose either Connected proxy (Managed by Orchestrator) or Disconnected proxy (Managed by the proxy service).
- Donnez un nom à votre proxy.
- Ajoutez l'URL relative à la machine virtuelle incluse dans la configuration du Orchestrator Credentials Proxy.
- Ajoutez la clé.
Pour le proxy connecté, selon la méthode d'installation, il s'agit soit de la clé secrète générée par le programme d'installation .msi, soit celle détenue par le paramètre Jwt:Keys.
Pour le proxy déconnecté, il doit s'agir d'une clé qui existe déjà dans l'un des fichiers de configuration locaux du proxy déconnecté.
Les informations que vous fournissez aux étapes 4 et 5 créent le lien entre Orchestrator et l'installation qui contient vos plug-ins de magasin d'informations d'identification personnalisés.
- Sélectionnez Créer.
Vous pouvez ensuite ajouter le magasin souhaité comme suit :
- At the tenant level, select Credentials > Stores > Add credential store to add a credential store.
- From the Proxy list, select the proxy that you have just created.
- From the Type list, select the third party credential store defined by your plugin.
- Fournissez la clé de configuration correspondant à celle du fichier de configuration local du proxy.
Remarque :
For disconnected setups, make sure that the keys used in Orchestrator match those defined in the proxy configuration file. For connected setups, Orchestrator manages the configurations automatically.
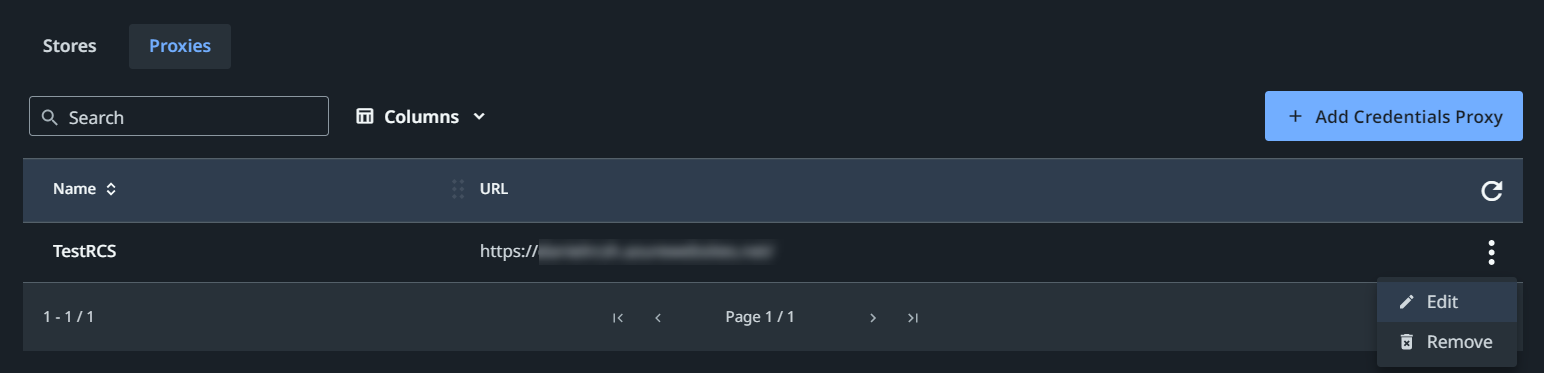
Editing a credentials proxy
To edit a proxy, click More Actions > Edit. The Edit Credentials Proxy page is displayed, allowing you to change the name, URL, or key as needed.
Supprimer Credentials Proxy
To delete a proxy, select More Actions > Remove. If the selected proxy is in use, a warning dialog is displayed, listing the number of robots and assets that will be affected. Select Yes to confirm the removal or No to abort.
Figure 4. Proxies tab
- Type de proxy
- Configuration déconnectée
- Configurations du magasin sécurisé
- Validation au démarrage
- Paramètres du niveau proxy
- Exemples de tests de configuration
- Exemple 1 : basique
- Exemple 2 : journaux supplémentaires et plusieurs configurations
- Exemple 3 : chemin d'accès personnalisé au journal et InMemoryStore
- Création d'un Credentials Proxy
- Editing a credentials proxy
- Supprimer Credentials Proxy