- Primeros pasos
- Mejores prácticas
- Tenant
- Acerca del contexto de tenant
- Buscar recursos en un tenant
- Gestionar robots
- Conexión de los robots a Orchestrator
- Almacenar credenciales de robots en CyberArk
- Almacenar contraseñas de robots desatendidos en Azure Key Vault (solo lectura)
- Almacenar las credenciales de robots desatendidos en HashiCorp Vault (solo lectura)
- Almacenamiento de credenciales de Unattended Robot en AWS Secrets Manager (solo lectura)
- Eliminar sesiones desconectadas y sin respuesta no atendidas
- Autenticación de Robot
- Autenticación de robots con credenciales de cliente
- Configurar las capacidades de automatización
- Soluciones
- Auditoría
- Configuración
- Cloud Robots
- Ejecución de automatizaciones unattended utilizando robots en la nube: VM
- Cargar tu propia imagen
- Reutilizar imágenes de máquina personalizadas (para grupos manuales)
- Restablecer credenciales para una máquina (para grupos manuales)
- Supervisión
- Actualizaciones de seguridad
- Pedir una prueba
- Preguntas frecuentes
- Configuración de VPN para robots en la nube
- Configurar una conexión de ExpressRoute
- Transmisión en vivo y control remoto
- Automation Suite Robots
- Contexto de carpetas
- Procesos
- Trabajos
- Apps
- Desencadenadores
- Registros
- Supervisión
- Índices
- Colas
- Activos
- Sobre los activos
- Gestión de Activos en Orchestrator
- Gestión de Activos en Studio
- Almacenar activos en Azure Key Vault (solo lectura)
- Almacenamiento de activos en HashiCorp Vault (solo lectura)
- Almacenamiento de activos en AWS Secrets Manager (solo lectura)
- Almacenamiento de activos en Google Secret Manager (solo lectura)
- Conexiones
- Reglas empresariales
- Depósitos de almacenamiento
- Servidores MCP
- Pruebas de Orchestrator
- Servicio de catálogo de recursos
- Integraciones
- Solución de problemas

Guía del usuario de Orchestrator
Managing credential proxies
Puedes crear y administrar proxies para tus propios almacenes de credenciales personalizadas, lo que te permite controlar individualmente la seguridad de tus credenciales.
Tipos de proxy
Puedes elegir entre estos dos tipos:
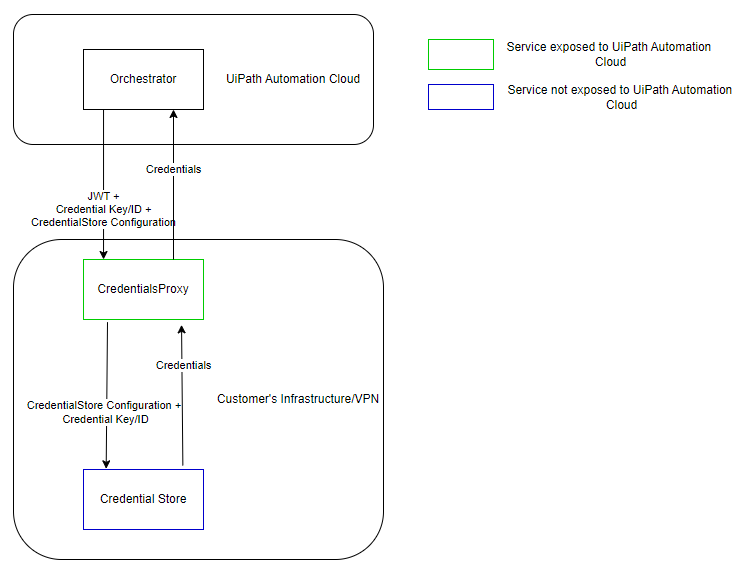
- Connected proxy (Managed by Orchestrator)
- when a robot requests credentials, Orchestrator retrieves them from the proxy and passes them on to the robot.
Figure 1. Connected proxy architecture
- Disconnected proxy (Managed by the proxy service) - when a robot requests credentials, they are retrieved directly from the proxy, without having to go through Orchestrator. This type is only compatible with Robots version 23.10+.
Figure 2. Disconnected proxy architecture 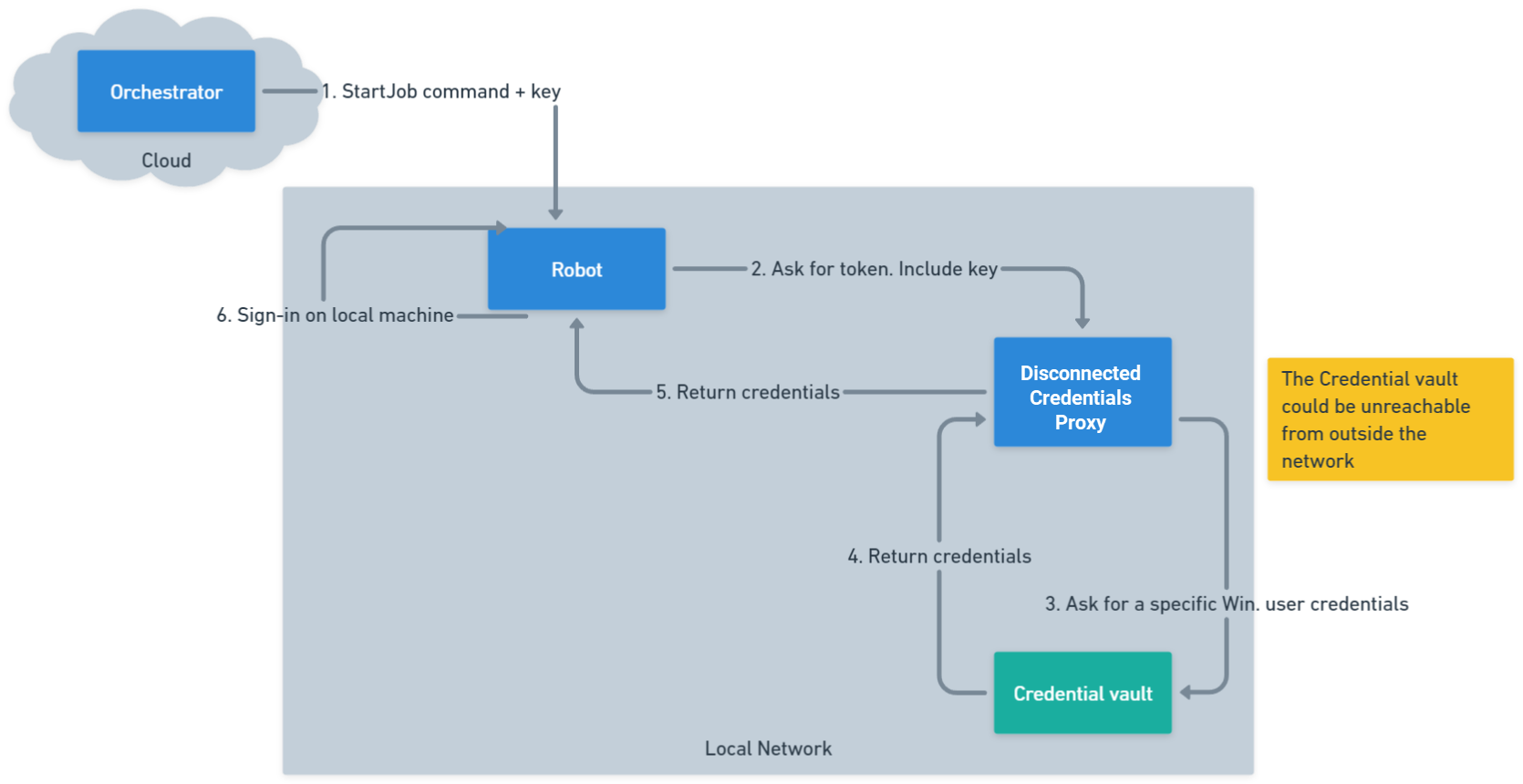
- The disconnected credentials proxy is only available if you are on the Enterprise - Advanced licensing plan.
- If you want to retrieve disconnected proxy credentials, you need to use the following minimum versions: 2.0.1 for the proxy, and 24.3 for the System Activities pack.
Configuración desconectada
El proxy de credenciales de Orchestrator en la variante desconectada funciona de forma similar a la configuración conectada, con algunas diferencias clave.
Especifica en el archivo appsettings.json que el proxy debe iniciarse en su modo desconectado. Para hacer esto, bajo AppSettings establece el parámetro CredentialsProxyType con el valor Disconnected.
Esto le dirá al proxy que haga las cosas de forma un poco diferente al iniciar y que lea su configuración de almacén seguro en el archivo appsettings.json. Si falta el parámetro o el valor es diferente, el proxy se iniciará en su modo conectado.
Especifica en el archivo appsettings.json que el proxy debe iniciarse en su modo desconectado. Para hacer esto, bajo AppSettings establece el parámetro CredentialsProxyType con el valor Disconnected.
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
{
...
"AppSettings": {
...
"CredentialsProxyType": "Disconnected",
...
}
}
Esto le dirá al proxy que haga las cosas de forma un poco diferente al iniciar y que lea su configuración de almacén seguro del archivoappsettings.json. Si falta el parámetro o el valor es diferente, el proxy se iniciará en su modo conectado.
Configuraciones de almacén seguro
Cada entrada de configuración debe contener:
- Key: unique identifier used in Orchestrator when linking stores. This must be unique in the list of configurations
- Type: the type of secure store (such as Azure Key Vault, BeyondTrust, CyberArk, HashiCorp Vault, InMemory, and others).
- Context: the data needed by the Secure Store implementation, which varies depending on the store type.
Consulta el siguiente ejemplo de configuración de almacén seguro:
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
{
...
"AppSettings": {
...
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "{someUri}",
"DirectoryId": "{someDirectoryId}",
"ClientId": "{someClientId}",
"ClientSecret": "{someClientSecret}"
}
},
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "{someHost}",
"APIRegistrationKey": "{someApiKey}",
"APIRunAsUsername": "{someApiUsername}",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
...
}
}
The SecureStoreConfigurations parameter is an array of configurations so you can have as many configurations as you want. Multiple configurations of the same type are supported, as long as the Key values are unique.
Validación de inicio
Al ejecutarse en modo desconectado, el proxy realiza la validación al iniciarse:
- Valida que existen las configuraciones necesarias en
appsettings.json. - Verifica que no se encuentren claves duplicadas en
SecureStoreConfigurations. - Confirma que todos los valores
Typeson válidos. - Valida la conectividad de almacén (llamadas
ValidateContextAsyncpara cada almacén).
Configuración de nivel de proxy
Algunos almacenes de credenciales seguros requieren configuración en el nivel de host que debe especificarse en appsettings.Production.json:
- CyberArk: settings like
CLIPasswordSDKExePath,UsePowerShellCLI, andAdditionalAllowedCharactersmust be defined underAppSettings.{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArk.CLIPasswordSDKExePath": "D:\\SomePath\\CLIPasswordSDK.exe", // ... } // ... } - CyberArkCCP: may require
Plugins.SecureStores.CyberArkCCP.KeyStorageFlags = "MachineKeySet".{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }{ // ... "AppSettings": { "Plugins.SecureStores.CyberArkCCP.KeyStorageFlags": "MachineKeySet", // ... } // ... }
Configuration test examples
Consulta los siguientes ejemplos prácticos appsettings.Production.json.
Antes de realizar cualquier cambio en el archivo appsettings.Production.json, asegúrate de crear una copia de seguridad del archivo original. Esto te permite restaurar fácilmente la configuración inicial o comparar los cambios si surgen incidencias durante la configuración.
Ejemplo 1: básico
Configuración con BeyondTrust y Azure Key Vault:
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
{
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname",
"APIRegistrationKey": "<APIRegistrationKey",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
}
]
}
}
Ejemplo 2: registros adicionales y varias configuraciones
Incluye varios almacenes y registro avanzado.
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
{
"Logging": {
"LogLevel": {
"Default": "Trace",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information",
"Microsoft.AspNetCore.HttpLogging.HttpLoggingMiddleware": "Information"
}
},
"Jwt": {
"Keys": [ "<YourKey>" ]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
// AzureKeyVault owned by <username>; contact for more info
// Robot externalName: "<name>"
// The expected value of this secret is "<name>"
{
"Key": "SecureStoreKey1",
"Type": "AzureKeyVault (read only)",
"Context": {
"KeyVaultUri": "<VaultURL>",
"DirectoryId": "<DirectoryID>",
"ClientId": "<ClientID>",
"ClientSecret": "<ClientSecret>"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey2",
"Type": "BeyondTrust Password Safe - Managed Accounts",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"DefaultManagedSystemName": "",
"SystemAccountDelimiter": "/",
"ManagedAccountType": "system"
}
},
// In case this fails, check our internal documentation on checking if BeyondTrust is down
// <InternalDocsURL>
// Robot externalName: "<ExternalName>"
{
"Key": "SecureStoreKey3",
"Type": "BeyondTrust Password Safe - Team Passwords",
"Context": {
"Hostname": "<Hostname>",
"APIRegistrationKey": "<APIRegistrationKey>",
"APIRunAsUsername": "<Username>",
"FolderPathPrefix": "/", // default is "/", but it can be changed to anything
"FolderPasswordDelimiter": "/" // default is "/", but it can be changed to anything
}
},
{
// asset external name: Operating System-WinDomain
// password: <password>
"Key": "SecureStoreKey1",
"Type": "CyberArk Conjur Cloud (read only)",
"Context": {
"ServiceUrl": "<ServiceURL>",
"LoginName": "<LoginName>",
"ApiKey": "<APIKey>",
"VariableIdPrefix": "data/vault/Safe"
}
},
// Must have an empty context
// No values on startup; should add values using the endpoints before trying trying to get anything
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {
}
}
]
}
}
Ejemplo 3: ruta de registro personalizada e InMemoryStore
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
{
"NLog": {
"throwConfigExceptions": true,
"targets": {
"logfile": {
"type": "File",
"maxArchiveFiles": 180,
"fileName": "<FileName>",
"layout": "${longdate} ${logger} ${message}${onexception:${newline}${exception:maxInnerExceptionLevel=10:format=shortType,message,stacktrace:separator=*:innerExceptionSeparator=
	}}"
}
},
"rules": [
{
"logger": "*",
"minLevel": "Information",
"writeTo": "logconsole,logfile,eventLog"
}
]
},
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft.AspNetCore": "Warning"
}
},
"Jwt": {
"Keys": [
"<YourKey>"
]
},
"AppSettings": {
"Plugins.SecureStores": "UiPath.Orchestrator.CyberArk.dll;UiPath.Orchestrator.AzureKeyVault.SecureStore.dll;UiPath.Orchestrator.SecureStore.CyberArkCCP.dll;UiPath.Orchestrator.SecureStore.CyberArkConjur.dll;UiPath.Orchestrator.SecureStore.HashiCorpVault.dll;UiPath.Orchestrator.SecureStore.ThycoticSecretServer.dll;UiPath.Orchestrator.SecureStore.BeyondTrust.dll;UiPath.Orchestrator.SecureStore.AWSSecretsManager.dll",
"UseInMemorySecureStore": "true",
"CredentialsProxyType": "Disconnected",
"SecureStoreConfigurations": [
{
"Key": "InMemoryKey1",
"Type": "InMemorySecureStore",
"Context": {}
}
]
}
}
Creación de un proxy de credenciales
Once you have installed the Orchestrator Credentials Proxy, you can create a custom proxy, which holds your custom credential stores.
Figure 3. Add Credentials Proxy page 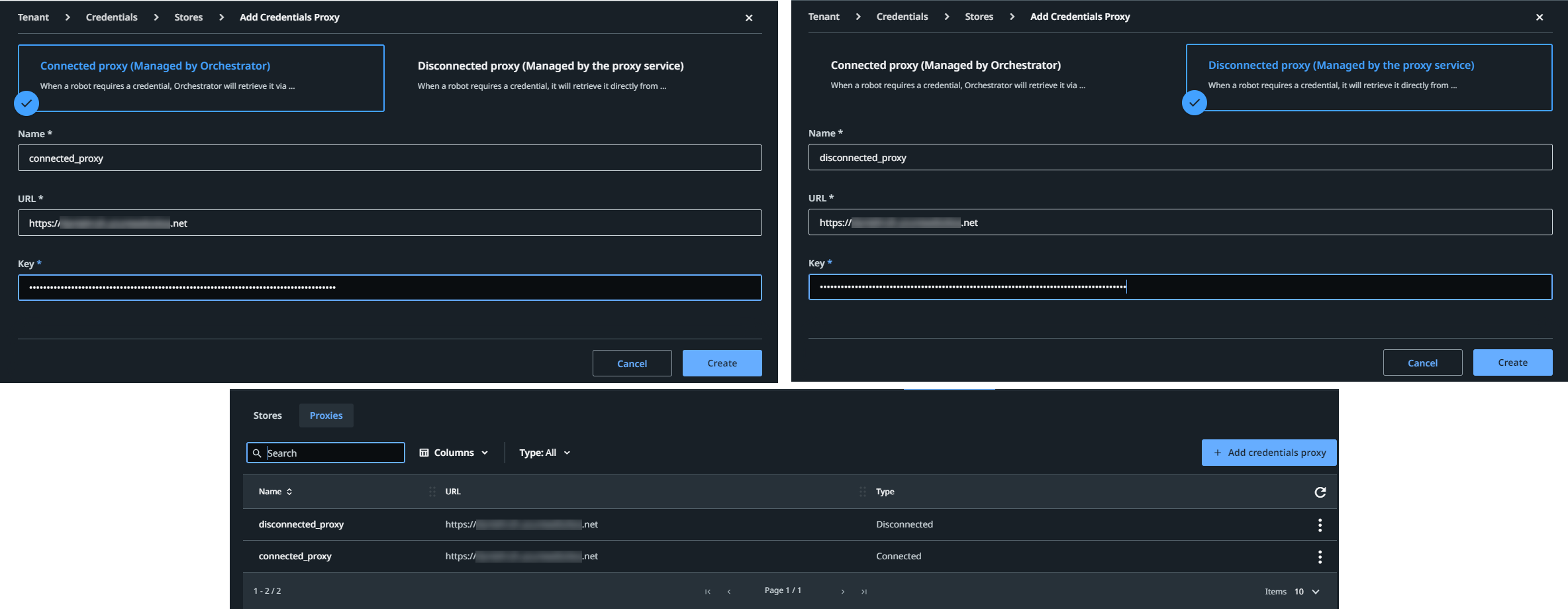
Para ello, sigue los siguientes pasos:
- At the tenant level, select Credentials > Proxies > Add Credentials Proxy. The Add Credentials Proxy window is displayed.
- Choose either Connected proxy (Managed by Orchestrator) or Disconnected proxy (Managed by the proxy service).
- Agregue un nombre para su proxy.
- Añade la URL perteneciente a la máquina virtual incluida en la configuración del proxy de credenciales de Orchestrator.
- Añade la clave.
Para el proxy conectado, dependiendo del método de instalación, esta es la clave secreta generada por el instalador .msi o la que está asociada al parámetro Jwt:Keys.
Para el proxy desconectado, debe ser una clave que ya existe en uno de los archivos de configuración local del proxy desconectado.
La información que proporcionas en los pasos 4 y 5 crea el enlace entre Orchestrator y la instalación que contiene tus complementos de almacén de credenciales personalizados.
- Selecciona Crear.
A continuación, puedes añadir el almacén deseado de la siguiente manera:
- At the tenant level, select Credentials > Stores > Add credential store to add a credential store.
- From the Proxy list, select the proxy that you have just created.
- From the Type list, select the third party credential store defined by your plugin.
- Proporciona la misma clave de configuración que la del archivo de configuración local del proxy.
Nota:
For disconnected setups, make sure that the keys used in Orchestrator match those defined in the proxy configuration file. For connected setups, Orchestrator manages the configurations automatically.
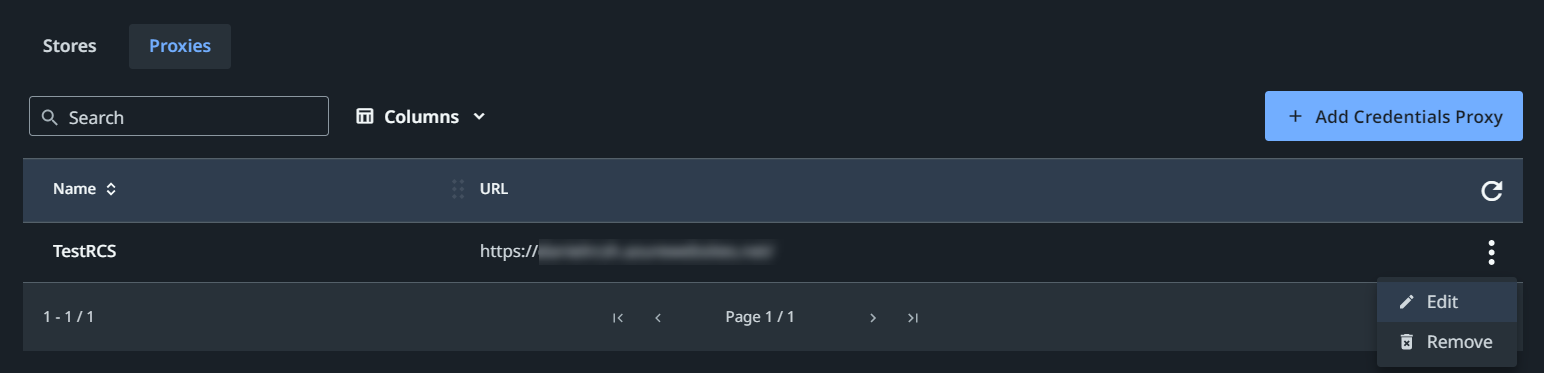
Editing a credentials proxy
To edit a proxy, click More Actions > Edit. The Edit Credentials Proxy page is displayed, allowing you to change the name, URL, or key as needed.
Eliminar un proxy de credenciales
To delete a proxy, select More Actions > Remove. If the selected proxy is in use, a warning dialog is displayed, listing the number of robots and assets that will be affected. Select Yes to confirm the removal or No to abort.
Figure 4. Proxies tab
- Tipos de proxy
- Configuración desconectada
- Configuraciones de almacén seguro
- Validación de inicio
- Configuración de nivel de proxy
- Ejemplos de prueba de configuración
- Ejemplo 1: básico
- Ejemplo 2: registros adicionales y varias configuraciones
- Ejemplo 3: ruta de registro personalizada e InMemoryStore
- Creación de un proxy de credenciales
- Editing a credentials proxy
- Eliminar un proxy de credenciales