- Getting started
- Best practices
- Tenant
- About the Tenant Context
- Searching for Resources in a Tenant
- Managing Robots
- Connecting Robots to Orchestrator
- Storing Robot Credentials in CyberArk
- Storing Unattended Robot Passwords in Azure Key Vault (read only)
- Storing Unattended Robot Credentials in HashiCorp Vault (read only)
- Storing Unattended Robot Credentials in AWS Secrets Manager (read only)
- Deleting Disconnected and Unresponsive Unattended Sessions
- Robot Authentication
- Robot Authentication With Client Credentials
- SmartCard Authentication
- Configuring automation capabilities
- Audit
- Settings - Tenant Level
- Resource Catalog Service
- Folders Context
- Automations
- Processes
- Jobs
- Triggers
- Logs
- Monitoring
- Queues
- Assets
- Storage Buckets
- Orchestrator testing
- Other Configurations
- Integrations
- Host administration
- Organization administration
- Troubleshooting

Orchestrator user guide
Storing Robot Credentials in CyberArk
Before beginning the procedures below, make sure you have configured your CyberArk® integration.
Adding Accounts for Your Robots
You must add the login credentials under which your Robot runs. If you have multiple Robots, perform this procedure for all of them. This procedure applies to both local and domain users. From the CyberArk® PVWA interface, follow these steps:
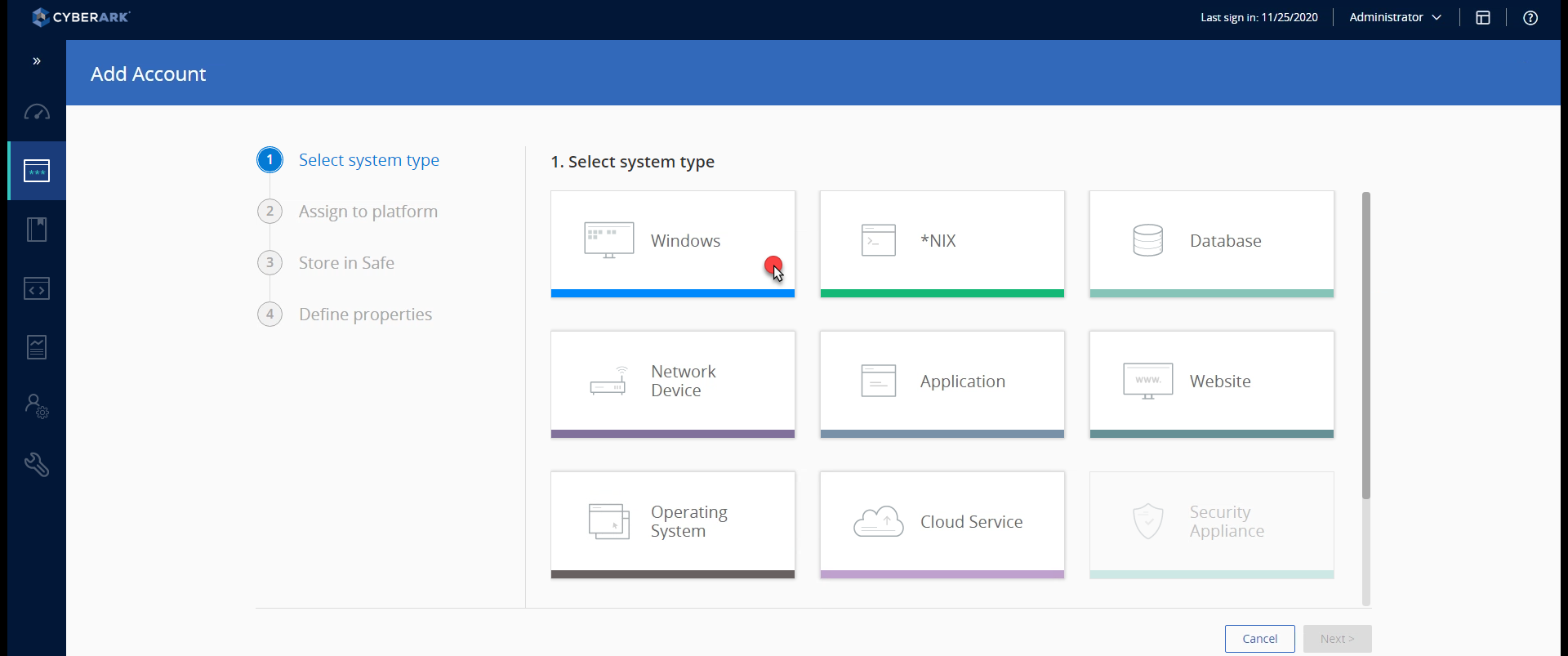
- On the Accounts tab, click Add Account. The Add Account page is displayed.
- Select Windows in the System Type list.
Figure 1. Selecting Windows in the system type list
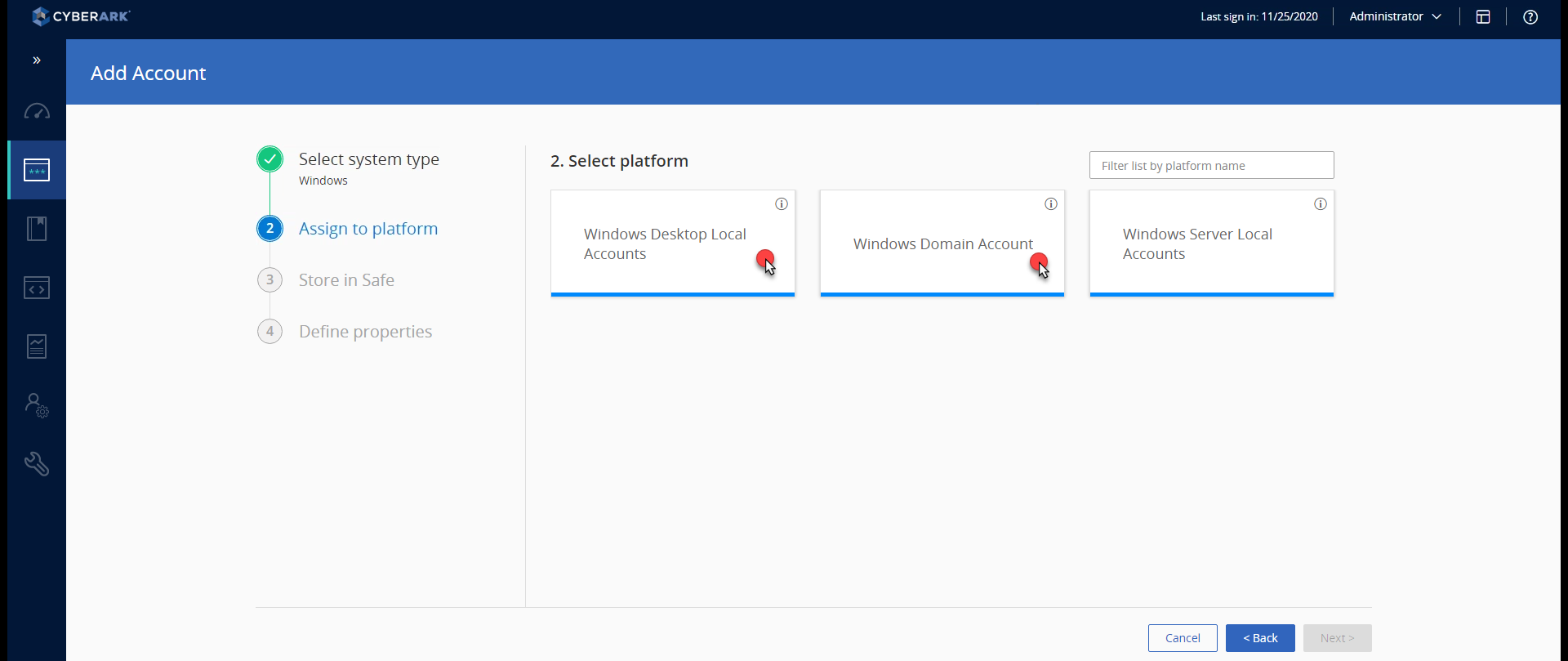
- On the Assign to Platform tab:
- select Windows Desktop Local Accounts if the Robot user is local.
- select Windows Domain Account if the Robot user is part of an Active Directory.
Figure 2. Selecting the platform
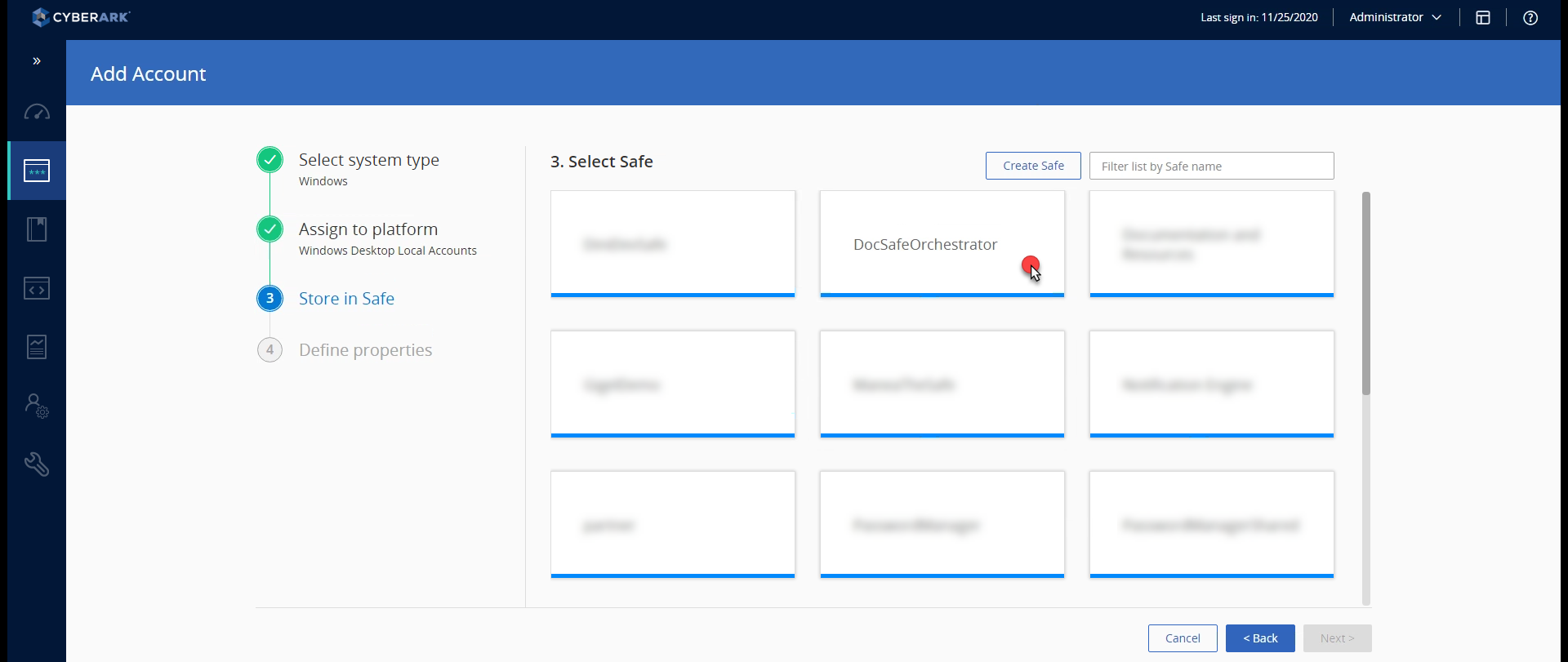
- On the Store in Safe tab, select the safe you previously created.
Figure 3. Selecting the safe
- On the Define Properties tab, populate the following fields:
Figure 4. Defining account properties
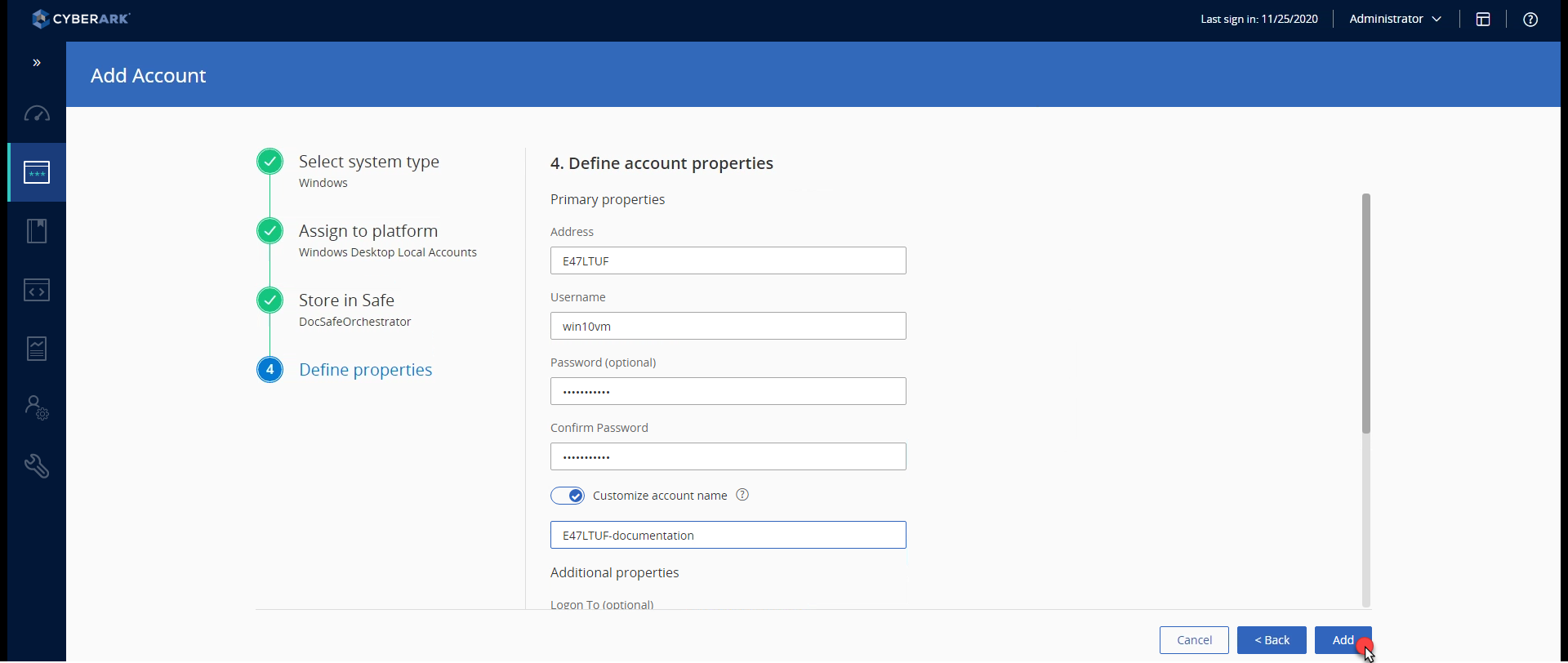
| Field | Value |
|---|---|
| Address |
|
| Username | The name of the account under which the Robot runs. |
| Password and Confirm Password | Type the password that belongs to the account under which the Robot runs. |
| Customize Account Name Toggle | Enabled. Type the machine or domain name, and the Robot username. The same name needs to be used in Orchestrator when defining the credential for the robot. |
- Click Save. The account is saved. Orchestrator uses this to retrieve the Robot credentials when it needs to, if you have the Robot provisioned in Orchestrator.
Retrieving the Vault Credentials
After performing the steps above, you have to provision the Robot in Orchestrator. As you are now using CyberArk® to store your passwords, please note that in the Provision Robot window, you no longer have to add the password. However, the user is still mandatory.
When provisioning the Robot in Orchestrator, add the username as you normally would:
- for local users - the actual username, such as
Documentation; - for domain users - the username and domain it runs under, in the
DOMAIN\usernameformat, such asuipath\administrator.
Based on the account provided for the Robot, Orchestrator searches for a match in CyberArk. When a match is found, the corresponding password is retrieved.
- When making changes to the password in Cyberark Application Password Provider, please keep in mind that it might take a few minutes for it to be propagated in Orchestrator due to AIM's cache system.
- When a robot or asset is created in Orchestrator, it is linked to an existing secret using the Orchestrator asset's External Name. Make sure that the CyberArk account name is set in the External Name field, to be mapped with the CyberArk account details.